Phishing Spam Fraud Malware Security Forms Security Assessments Security Tips MFA VPN
IT Security
Reporting to the Vice President CIO/CTO, the goal of the Information Security Office is to protect confidentiality, integrity, and availability of information technology resources and assets at The University of Toledo. Protection of these resources allows the university to reach designated educational, operational and research goals. All University members share responsibility to help achieve the University mission. Some of the services our office provides are:
- Security risk assessments/reviews
- Vulnerability assessment and remediation consultation
- Incident response
- Security Awareness
- SPAM identification
Phishing Email
When you are using the Microsoft Office Client, please report any phishing emails
by using the report message icon on your Outlook toolbar.![]()
If you are using the web client, please report any phishing emails by using the junk icon on your Outlook toolbar.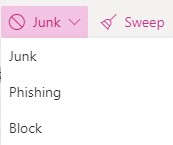
The Outlook Mobile App has a report junk option when you open the message and click
"..." and select report junk. You can then select whether you believe the message is junk
or phishing.
If a user is not using any Outlook clients, (Desktop/OWA/Mobile), they will not have
the button. If the button is not available, forward the message to emailabuse@utoledo.edu.
If you think your account has been compromised, change your password immediately by going to UTAD Account Password Reset.
Security Alerts
- Job Offer Phishing Email - A number of people have received emails with the words in the subject line, URGENT STUDENT NOTICE !!
- Check Scam/UT Online Directory: - IT Security and the University of Toledo Police Department have been alerted to a recent scam. UT resources are receiving checks in the mail with a letter assigning them a task. This scam is unique because it involves a tangible item (letter instead of an email) and an online item (information that is available in our online directory).
- Recent Phishing Emails and Their Subject Line: - Evaluations, Urgent Tasks, Notice of Benefits Enrollment, COVID-19 Assessment, Direct Deposit Notification, FAX Messages, Give Me Your Cell Number, Let Me Know If You Are Free At The Moment, Scheduled Maintenance of the UTAD Portal.
- Memo From HR Phishing Emails - A number of people have received emails telling them that they have a message from the Human Resource Department and to click the link to view the message. Do not click on the link and provide your personal information.
- Action Required Scam Emails - A number of people have received emails telling them that they are being notified that someone has logged into their email from another device. The email asks that you confirm your account by clicking on the link. Do not click on the link and provide your personal information.
- Part Time Job Offer Scam Emails - A number of people have received emails telling them about a fake insurance job they have available and to click on the link below to apply. Unexpected job offers are often scams. Do not click on the link and provide your personal information.
- Gift Card Scam Emails - We continue to be made aware that emails about gift cards continue to populate inboxes. This is just a reminder to continue being alert to these scams and do not respond to it. Visit our phishing page to see past phishing emails.
- Nanny/Babysitting Scam - A recent attempt to offer a nanny or babysitting job.


